Deploying Kubernetes Dashboard with Argo/Kustomize
Deploying the Kubernetes Dashboard through Argo and Kustomize with ingress and a service account.
My new cluster is coming along, next on the list is deploying the Kubernetes Dashboard through Argo and Kustomize with ingress and a service account.
I am managing my cluster using Argo CD and, so far, primarily using Kustomize. Next on my list of things to get in the cluster is the dashboard. I like to see what is going on in my cluster.
I am adding 2 things to my deployment. First is an ingress so I can access it without using the proxy from kubectl. That is just annoying. The second is a service account that I can use to access the dashboard.
There are 3 files in the following layout.
base
- ingress.yaml
- serviceaccount-admin.yaml
kustomization.yaml
The ingress.yaml file contains the ingress object. The serviceaccount-admin.yaml file contains the admin service account and cluster role binding object so it can access the cluster. kustomization.yaml contains my Kustomize configuration and glues it all together.
The namespace I am using is kubernetes-dashboard. If you want to use a different namespace you will need to update it in the cluster role binding in serviceaccount-admin.yaml.
ingress.yaml
For the ingress to work you need to tell it to communicate to the backend as https. I am currently using the NGINX ingress controller with defaults, so the property annotation is nginx.ingress.kubernetes.io/backend-protocol set to HTTPS. Your environment may be different.
Here is the full contents:
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: kubernetes-dashboard
annotations:
ingress.kubernetes.io/proxy-body-size: 100M
ingress.kubernetes.io/app-root: "/"
nginx.ingress.kubernetes.io/backend-protocol: "HTTPS"
spec:
rules:
- host: kubedashboard.example.com
http:
paths:
- backend:
service:
name: kubernetes-dashboard
port:
number: 443
path: /
pathType: ImplementationSpecific
tls:
- hosts:
- kubedashboard.example.com
serviceaccount-admin.yaml
This contains our service account for the token and the cluster role binding to give it permissions to the cluster so you can see and do everything in the dashboard.
apiVersion: v1
kind: ServiceAccount
metadata:
name: dashboard-admin-sa
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: dashboard-admin-sa
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: dashboard-admin-sa
namespace: kubernetes-dashboard
kustomization.yaml
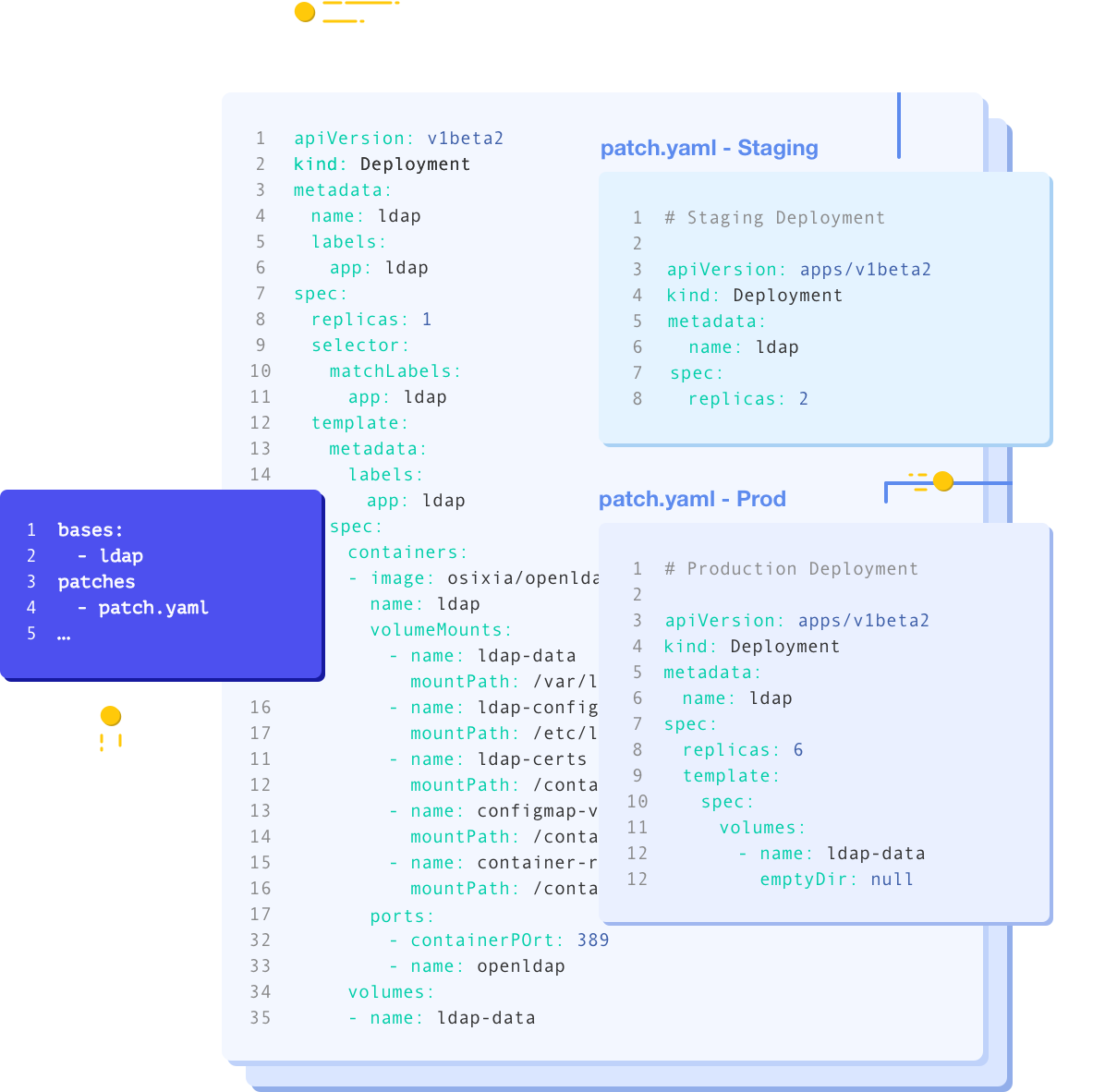
This file glues everything together into a nice bundle. It references the current deployment file in the master branch for the Kubernetes Dashboard. It is a simple Kustomize file.
apiVersion: kustomize.config.k8s.io/v1beta1
kind: Kustomization
resources:
- base/ingress.yaml
- base/serviceaccount-admin.yaml
- https://raw.githubusercontent.com/kubernetes/dashboard/master/aio/deploy/recommended.yaml
namespace: kubernetes-dashboard
Dashboard authentication
To get the token for the dashboard, you'll first get a list of the secrets, then get the secret data from the one that starts with dashboard-admin-sa-token
kubectl get secrets -n kubernetes-dashboard
That will return something like this:
NAME TYPE DATA AGE
dashboard-admin-sa-token-rxw54 kubernetes.io/service-account-token 3 23m
default-token-snpfp kubernetes.io/service-account-token 3 23h
kubernetes-dashboard-certs Opaque 0 23h
kubernetes-dashboard-csrf Opaque 1 23h
kubernetes-dashboard-key-holder Opaque 2 23h
kubernetes-dashboard-token-tnh7m kubernetes.io/service-account-token 3 23h
My token is stored in the dashboard-admin-sa-token-rxw54 secret.
kubectl get secret dashboard-admin-sa-token-rxw54 -n kubernetes-dashboard -o jsonpath='{.data.token}' | base64 -d
That command will spit out the token to use when authenticating to the dashboard.
Argo CD
There was nothing special in getting Argo to recognize and deploy the dashboard. It just worked after creating the application and pointing it to the correct path.
Conclusion
This didn't take too long to figure out, but there wasn't any guidance on using Kustomize to deploy the dashboard. Everything just said run kubectl apply. I do not like running kubectl apply to deploy an application. I like automation and repeatability.
I thought I was going to need to have Argo exclude the secret path when sync'ing the service account. But I did not. It was smart enough to take that in to account already. Cool.
Links